The Architecture of Fragility: Engineering in the Era of Extreme Technology
The 2026 paradox: trillions in AI vs. fragile code. Explore the Axios crisis, AI immune systems, and the shift to zero-trust dev.
1. The Paradox of 2026
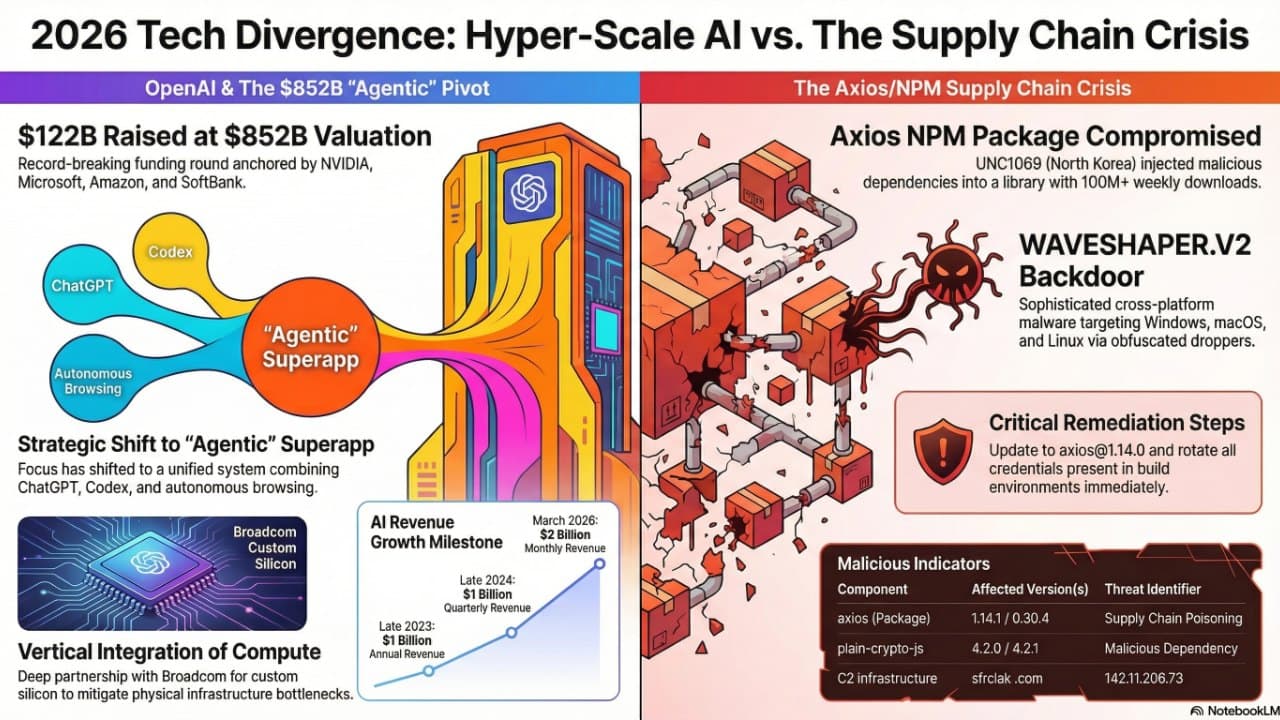
We have entered the era of "Extreme Technology." In late March 2026, the industry witnessed a staggering divergence: OpenAI reached a valuation of $852 billion, while the global digital economy was simultaneously threatened by a single compromised dependency in the Axios library. This is the paradox of 2026: we have the capital to redesign the physical power grid, yet we remain structurally vulnerable to a few lines of malicious JavaScript in an NPM postinstall hook.
2. The Axios Compromise: Trust as a High-Risk Asset
The most urgent engineering reality of Q1 2026 is the sophisticated supply chain attack on the Axios library (over 100 million weekly downloads).
- The Actor: Attributed to the North Korea-nexus threat actor UNC1069.
- The Breach: A maintainer account was compromised to inject a malicious dependency,
plain-crypto-js@4.2.1, intoaxios@1.14.1andaxios@0.30.4. - The Payload: The attack deployed the SILKBELL dropper and the WAVESHAPER.V2 backdoor.
- Cross-Platform Impact: The backdoor delivers specific malicious files for Windows, macOS, and Linux, utilizing
wt.exeon Windows to evade detection. - C2 Communication: The malware beacons to
142.11.206.73on port 8000 every 60 seconds.
Remediation Steps
- Revert: Move immediately to
axios@1.14.0. - Audit: Check lockfiles for
plain-crypto-js. - Rotate: Assume environment compromise and rotate all API keys and credentials.
3. AI as a Synthetic Immune System
Manual code review is no longer sufficient against obfuscated threats. Cloudflare has responded with a two-stage AI pipeline to verify "code intent."
| Feature | Stage 1: GNN | Stage 2: LLM (gpt-oss-120b) |
|---|---|---|
| Input | Abstract Syntax Tree (AST) Structure | Deobfuscated Script & Context |
| Mechanism | Structural Pattern Matching | Semantic Intent Triage |
| Purpose | High-recall zero-day detection | High-precision false positive filtering |
| Latency | Minimal (3.5B scripts daily) | Higher (triggered by GNN) |
4. Efficiency and Infrastructure Scarcity
The AI industry is moving away from "model theater" toward utility. The primary constraint is now the "physics of power"—the global energy grid is physically capped, with connections in major hubs sold out through 2029. Companies are now pivoting toward custom silicon (like OpenAI’s partnership with Broadcom) to maximize "intelligence per watt."
5. Pruning the Attack Surface: Native Web Primitives
The web platform is evolving to absorb responsibilities previously held by third-party libraries, effectively reducing the external attack surface.
- Native Masonry (Safari 26.4): Implements
display: grid-lanes, removing the need for external layout libraries. - Scroll-Triggered Animations (Chrome 146): Offloads animations to worker threads via CSS.
- Modern Crypto (Node.js 25.9.0): Native support for TurboSHAKE and KangarooTwelve reduces reliance on external cryptographic packages.
6. Maintenance as Strategic Defense
"Boring" maintenance is now a top-tier security priority. State-sponsored actors actively monetize maintenance debt, making staying current a strategic necessity.
- Ruby 3.2 EOL: The final release (3.2.11) patched a critical
zlibvulnerability. - Rails Security: Emergency patches (7.2.3.1, 8.0.4.1, 8.1.2.1) addressed 10 CVEs, including high-impact Denial of Service (DoS) and Path Traversal risks.
7. Conclusion: The Zero-Trust Future
The engineering landscape of 2026 demands a radical shift in maturity. We operate in a world where a single npm install remains a potential "black swan" event. The path forward is a Zero-Trust Supply Chain: leveraging AI immune systems, pinning verified dependencies, and ruthlessly pruning third-party JavaScript footprints in favor of native browser primitives.
Comments
Sign in with Google or GitHub to comment.